Malware analysis Malicious activity
4.7
$ 26.50
In stock
(190)
Product Description
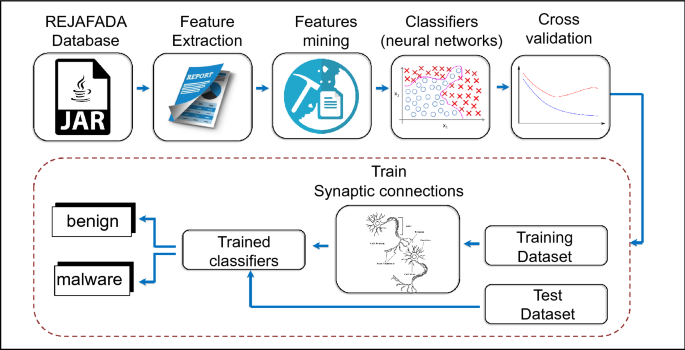
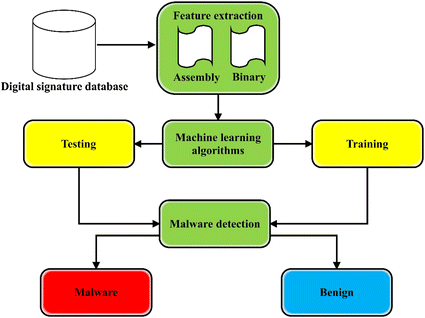
Antivirus applied to JAR malware detection based on runtime behaviors
Applied Sciences, Free Full-Text

Malware Analysis Explained - 's Cybersecurity Blog
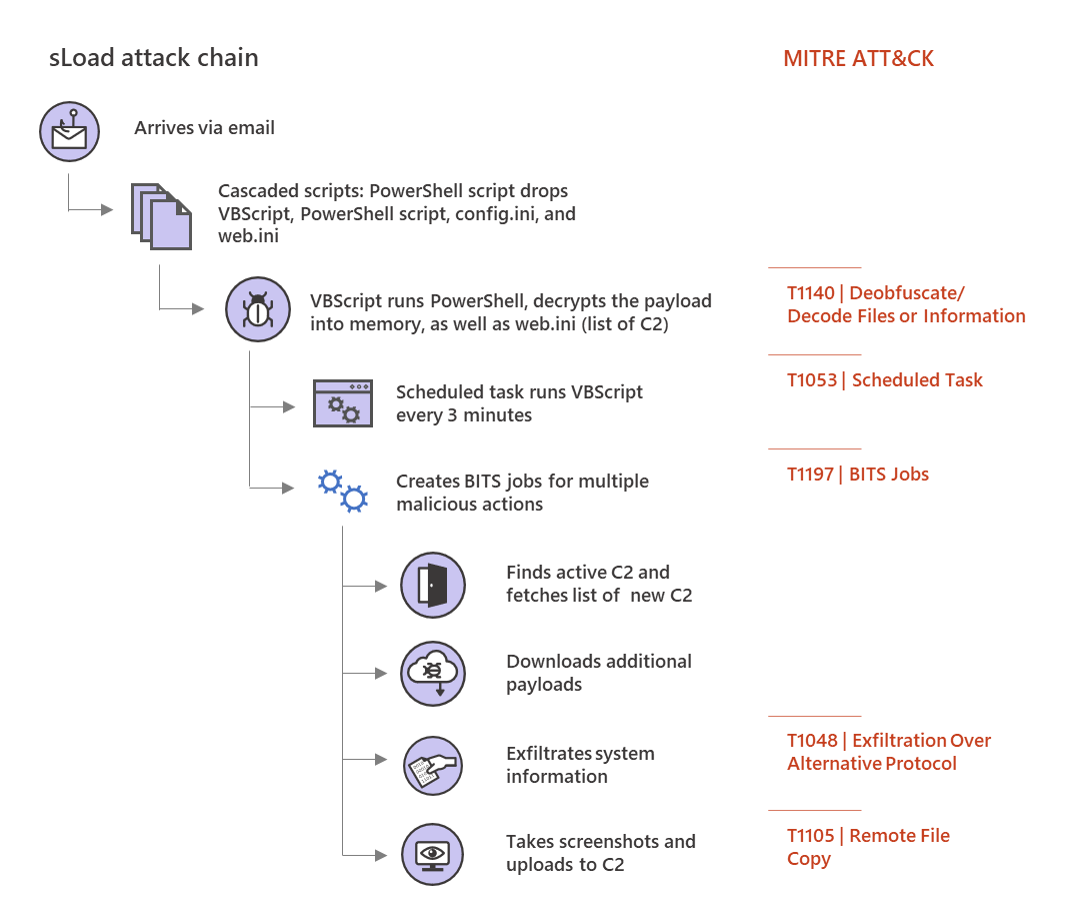
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities

Malware analysis: Hands-On Shellbot malware – Sysdig

Architecture of malware detection & classification approach
Applied Sciences, Free Full-Text
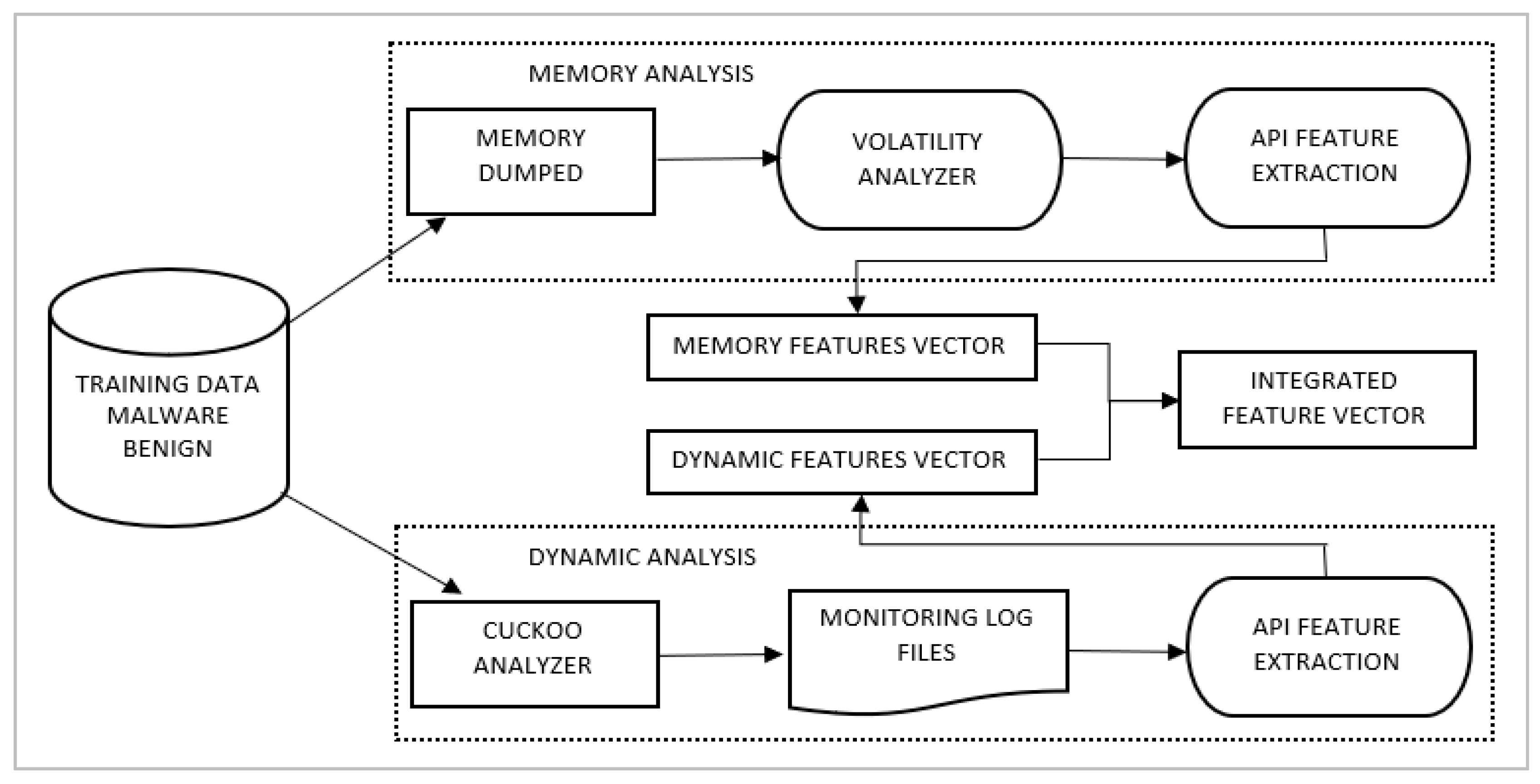
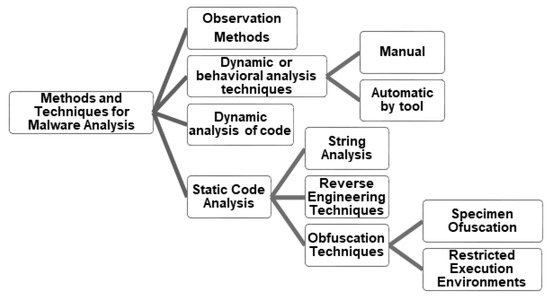
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences

Malware Analysis Of Malicious Documents

What to Include in a Malware Analysis Report

Election Security Spotlight – Malware Analysis

How to build a malware analysis sandbox with Elastic Security

Intro to Malware Analysis: What It Is & How It Works - InfoSec Insights

A Novel Approach to Detect Malware Based on API Call Sequence Analysis - Youngjoon Ki, Eunjin Kim, Huy Kang Kim, 2015

7 Benefits Of Dynamic Malware Analysis
![nflbite.com Website Traffic, Ranking, Analytics [August 2023] nflbite.com Website Traffic, Ranking, Analytics [August 2023]](https://cdn.semrush.com/__static__/semrush-logo-700.jpg)



/cdn.vox-cdn.com/uploads/chorus_asset/file/24213389/Philadelphia_1_111722.png)


